Table of Contents
DDoS attacks are one of the most persistent and costly threats facing businesses today. These attacks aim to overwhelm networks, servers, or applications with massive volumes of traffic, disrupting operations and damaging reputations. For companies operating online, understanding DDoS mitigation and implementing effective protection strategies is no longer optional—it’s essential.
In this guide, we’ll break down what DDoS mitigation is and why it matters. We’ll also answer common questions around DDoS attacks and mitigation techniques.
What is DDoS Mitigation?
DDoS mitigation refers to the processes, tools, and strategies used to protect a network, server, or application from a Distributed Denial of Service attack. In a typical DDoS attack, malicious actors send massive amounts of traffic from multiple sources to a target, aiming to saturate bandwidth, consume server resources, or exploit protocol weaknesses.
The goal of DDoS mitigation is to detect, absorb, and filter out this malicious traffic before it impacts legitimate users. Mitigation can be achieved through a combination of on-premises appliances, cloud-based services, or hybrid solutions, depending on the organization’s infrastructure and risk profile.
Modern DDoS mitigation solutions often operate across both the network layer (L3/L4) and the application layer (L7), addressing everything from volumetric floods to sophisticated attacks that mimic legitimate user behavior.
Why is DDoS Mitigation Important?
The consequences of failing to implement effective DDoS mitigation can be severe:
- Financial losses: Downtime caused by a DDoS attack can cost businesses thousands of dollars per minute. With attacks growing in frequency and intensity, unprotected organizations risk substantial revenue loss.
- Operational disruption: Critical business processes, online services, and customer-facing applications can be delayed or halted entirely, impacting productivity and service delivery.
- Reputational damage: Customers expect reliable online experiences. Frequent or prolonged outages due to DDoS attacks erode trust and may drive users to competitors.
- Increased security risk: Overwhelmed systems may expose vulnerabilities that attackers can exploit, potentially leading to data breaches or further attacks.
How DDoS Mitigation Works: Stages of Mitigation
Effective DDoS attack mitigation typically follows four stages: Detection, Diversion, Filtering, and Analysis. Each stage plays a critical role in ensuring attacks are neutralized quickly while minimizing impact on legitimate users.
Detection
Detection is the first and most crucial stage. Modern mitigation systems continuously monitor traffic to identify anomalies, including sudden spikes in requests, unusual IP distributions, protocol misuse, or suspicious behavior patterns.
Detection systems must balance sensitivity and accuracy:
- Too sensitive: Can generate false positives, blocking legitimate traffic.
- Not sensitive enough: Risks missing early attack signals.
Advanced solutions often leverage machine learning to establish baseline traffic patterns, providing early warning without disrupting normal users.
Diversion
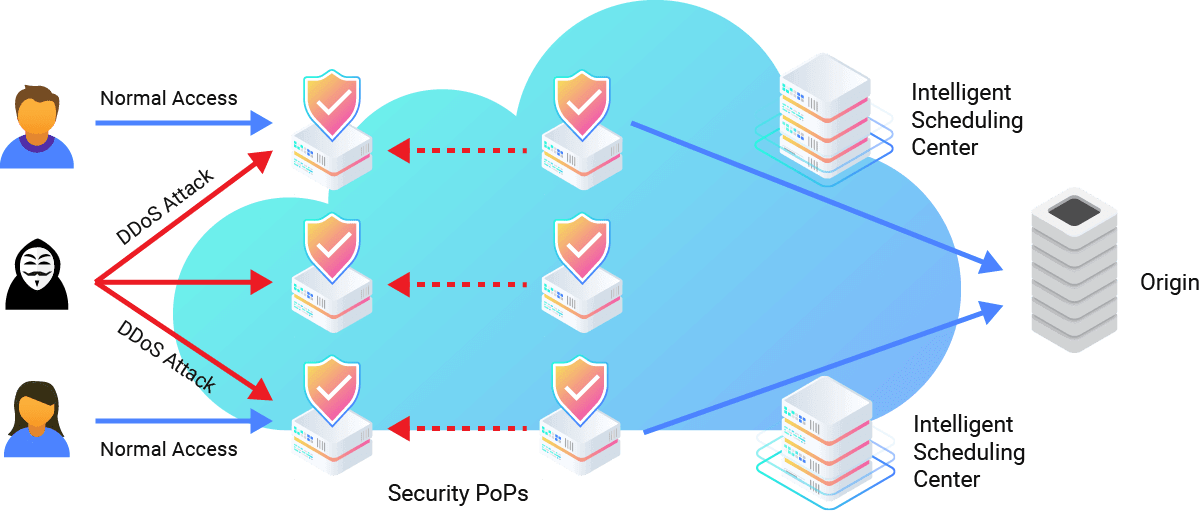
Once an attack is detected, the diversion stage ensures malicious traffic is redirected away from the core infrastructure. Traffic is routed to scrubbing centers or specialized nodes where it can be analyzed and processed.
Key objectives of diversion include:
- Protecting origin servers from overload
- Minimizing downtime for legitimate users
- Scaling dynamically to handle surges in traffic
Advanced cloud-based mitigation services distribute traffic across multiple points of presence (PoPs) to ensure no single node becomes overwhelmed.
Filtering
Filtering is where the system separates malicious traffic from legitimate requests. Techniques include:
- Deep packet inspection
- Rate limiting and throttling
- Behavioral and anomaly-based analysis
- Challenge-response verification for suspicious users
Effective filtering maintains low latency for genuine users while adapting in real-time to changing attack patterns, including multi-vector and application-layer attacks.
Analysis
Finally, analysis ensures lessons are learned from each attack. Security teams review traffic logs, study attack vectors, identify patterns, and refine mitigation rules.
Robust analysis enables proactive defense:
- Anticipating new attack methods
- Updating filtering policies dynamically
- Improving incident response for future attacks
Choosing a DDoS Mitigation Service
Selecting the right DDoS mitigation service provider is critical to a business’s security posture. Key factors to consider include:
Network Capacity
Mitigation providers should have sufficient bandwidth to absorb large-scale attacks. Cloud-based networks in the multi-terabit-per-second (Tbps) range offer significant headroom beyond what on-premises solutions can handle. Consider both raw capacity and geographical distribution of PoPs to align with your user base.
Processing Capacity
High packet-per-second (PPS) processing capabilities are essential to handle modern attacks, which can exceed 50 million PPS. Providers should ensure minimal latency while processing large volumes of traffic.
Latency and Time to Mitigation
Response speed is critical. Always-on protection can mitigate attacks within seconds, while on-demand solutions may introduce delays. Evaluate providers based on test scenarios and their ability to maintain service availability during attacks.
Multi-layered Protection
Effective mitigation addresses both:
- Network-layer attacks (L3/L4): Using techniques like null routing, sinkholing, advanced scrubbing, and IP masking.
- Application-layer attacks (L7): Employing behavioral analysis, machine learning, and challenge mechanisms to detect sophisticated attacks that mimic legitimate users.
How CDNetworks Can Help
CDNetworks provides enterprise-grade DDoS mitigation services designed to protect businesses against both network and application-layer attacks. Its Flood Shield 2.0 platform offers multi-layered protection across the full spectrum of DDoS threats, including volumetric attacks, application-layer attacks, and emerging zero-day or multi-vector attacks.
Key advantages include:
-
Global network capacity and infrastructure: Strategically placed PoPs and over 40 global scrubbing centers deliver more than 20 Tbps mitigation capacity, helping absorb volumetric DDoS attacks at the edge and maintaining uninterrupted business operations.
-
Multi-layered defense: Combines network-layer filtering (L3/L4), application-layer analysis (L7), advanced scrubbing, rate limiting, behavioral analysis, and machine learning to block HTTP floods, low-and-slow DDoS, and bot-driven campaigns.
-
Adaptive, AI-powered protection: The system continuously monitors network traffic, applies threat intelligence, and detects and mitigates known and emerging threats in real time. This minimizes false positives while keeping critical network infrastructure and data centers secure.
-
Cloud-based, scalable solutions: CDNetworks’ cloud DDoS mitigation architecture ensures always-on protection, filtering malicious traffic while letting legitimate users access services seamlessly. Solutions are flexible and can scale according to risk profiles.
-
24/7 expert support: Around-the-clock monitoring and rapid incident response ensure that attacks are neutralized quickly, protecting revenue, uptime, and brand reputation.
By combining network-layer and application-layer protection, global infrastructure, AI-driven analytics, and expert support, CDNetworks ensures critical assets—websites, APIs, and other digital platforms—remain operational even under large-scale DDoS attacks.
DDoS Mitigation FAQs
1. What is DDoS mitigation?
DDoS mitigation is the process of protecting networks, servers, and applications from Distributed Denial of Service attacks. It involves detecting, filtering, and managing malicious traffic to ensure legitimate users maintain uninterrupted access to digital services.
2. How can DDoS be prevented?
While no solution can fully prevent every DDoS attack, businesses can significantly reduce risk through a multi-layered strategy: monitoring traffic for anomalies, using cloud-based mitigation services, deploying web application firewalls (WAFs), implementing rate limiting, and maintaining network redundancy and excess bandwidth to absorb potential attacks. Explore our guide on DDoS prevention best practices and proactive defense strategies.
3. What is the common method used to mitigate DDoS attacks?
Common mitigation methods include traffic diversion to scrubbing centers, deep packet inspection and filtering, rate limiting, IP blacklisting, sinkholing, and challenge-response mechanisms for suspicious requests. Modern solutions often combine these techniques with machine learning and behavioral analysis to handle complex, multi-vector attacks.
4. What are the stages of DDoS mitigation?
Effective DDoS mitigation typically follows four stages:
- Detection– Identifying abnormal traffic patterns and early signs of attack.
- Diversion– Redirecting traffic to mitigation nodes or scrubbing centers.
- Filtering– Separating malicious traffic from legitimate traffic in real-time.
- Analysis– Reviewing attack data to refine defenses and prepare for future threats.
5. How do you choose a DDoS mitigation provider?
Key factors include network capacity, processing power, latency, global distribution of mitigation nodes, scalability, flexibility, and reliability. Providers should offer both network-layer and application-layer protection, as well as transparent pricing and 24/7 support to ensure rapid response during attacks.
6. How can CDNetworks mitigate DDoS?
CDNetworks delivers enterprise-grade DDoS mitigation by combining a global network of PoPs, real-time traffic monitoring, multi-layer filtering, and automated scrubbing. This approach ensures both network and application-layer attacks are absorbed or filtered, protecting websites, APIs, and other critical digital assets with minimal impact on legitimate users.
