Table of Contents
What Is a DDoS Attack?
A Distributed Denial of Service (DDoS) attack is a type of cyberattack that overwhelms a target system, network, or application with traffic. Attackers use large numbers of compromised devices to send traffic of requests simultaneously, making the service unavailable to legitimate users.
A simple way to visualize a DDoS attack is to imagine a small store with only one entrance. Under normal conditions, customers enter and exit smoothly. During a DDoS attack, thousands of coordinated fake customers simultaneously flood every entrance and occupy staff with meaningless requests. The mall itself remains intact, but legitimate shoppers can no longer access services because all available capacity is exhausted.
From a technical perspective, DDoS attacks are often analyzed through the lens of the OSI model, which describes how data moves through a network in layered stages.
Different DDoS attack types target different layers of this model, exhausting resources in distinct ways. Some attacks focus on flooding network bandwidth; others exploit weaknesses in network or transport protocols, while more sophisticated attacks operate at the application layer and closely resemble legitimate user behavior.
The sections below break down the major types of DDoS attack and clarify how they relate to specific layers and attack mechanisms.
What Is a Volumetric DDoS Attack (L3/L4)?
A volumetric DDoS attack overwhelms a target’s network capacity by flooding it with massive amounts of traffic. These attacks primarily target the network and transport layers of the OSI model (Layer 3 and Layer 4), focusing on exhausting bandwidth and routing resources rather than exploiting application logic.
They are commonly generated by large botnets, which allow attackers to send traffic floods from thousands or even millions of distributed sources. Because the traffic volume itself is the weapon, these attacks are usually measured in bits per second (bps) rather than by request count.
Think of it like a firehose blasting into a narrow water pipe. The sheer volume of water instantly fills the pipe, leaving no room for normal flow. In the same way, a volumetric attack saturates network links, so legitimate requests are effectively blocked.
Common examples of volumetric DDoS attacks include:
Despite their visibility, volumetric attacks remain highly effective at overwhelming network capacity and disrupting legitimate traffic.
What Is a Protocol DDoS Attack (L3/L4)?
A protocol DDoS attack targets weakness in network and transport protocols, exhausting server or network resources by forcing them to process abnormal or incomplete connections.
Similar to volumetric attacks, protocol attacks mainly operate at Layer 3 and Layer 4 of the OSI model. However, their objectives are different. Instead of consuming bandwidth, they aim to overload the systems responsible for managing connections, state tables, and packet handling.
You can think of a protocol attack as repeatedly dialing a customer service line and hanging up before the call is completed. Each call uses a small amount of system attention, but when thousands of such calls happen at once, the system can no longer respond to real customers. In the same way, protocol attacks drain finite connection resources until normal traffic is denied.
By exploiting the inherent design of network protocols, protocol attacks can achieve significant disruption even with relatively low traffic volumes, making them more difficult to detect than pure volumetric floods.
Common examples of protocol DDoS attacks include:
- SYN flood attacks
- ACK flood attacks
- TCP flood attacks
Even at relatively low traffic volumes, protocol attacks remain highly effective at exhausting connection resources and disrupting normal network operations.
What Is an Application Layer (Layer 7) DDoS Attack?
An application layer DDoS attack targets the top layer of the OSI model (Layer 7), focusing directly on web applications and services rather than network infrastructure. Instead of overwhelming bandwidth or protocol mechanisms, these attacks exhaust server resources by generating large volumes of seemingly legitimate HTTP or HTTPS requests. Because the traffic often mimics normal user behavior, distinguishing malicious activity from geniun usage becomes significantly more difficult.
Think of it like an online store where thousands of “shoppers” simultaneously add items to carts, search products, or refresh pages repeatedly. Each individual action is harmless, but at scale, automated requests can consume CPU, memory, and database connections, slowing or even crashing the service.
In contrast to volumetric or protocol attacks, application layer attacks are typically measured in requests per second (RPS) rather than bandwidth. They require fewer bots to be effective, but can cause severe disruption, especially to APIs, login systems, and search functions.
Common examples of application layer DDoS attacks include:
- HTTP GET/POST flood attacks
- Slowloris attacks
- XML-RPC flood attacks
- WordPress admin login flood attack
What Is the Difference Between DoS and DDoS?
The attacks described above all rely on distributed sources of traffic. However, not all denial-of-service (DoS) attacks are distributed.
A DoS attack is a type of attack that typically originates from a single source. Because the traffic comes from one machine or a limited range of IP addresses, it is often easier to detect and block.
A DDoS attack, by contrast, uses many compromised devices simultaneously. The distributed structure of a DDoS attack increases scale, resilience, and impact, making mitigation significantly more complex.
In essence, both attacks aim to disrupt availability, but DDoS achieves service disruption through coordinated distribution rather than a single attacking source.
What Is the Purpose of a DDoS Attack?
DDoS attacks vary in form and technical execution, but their underlying objective is consistent: disrupting availability.
Unlike intrusions that aim to gain unauthorized access or steal data, DDoS attacks focus on service interruption. When online services become slow or unreachable, the operational and reputational impact can be immediate.
In practice, organizations are targeted by DDoS attacks for several recurring reasons:
- Financial extortion: demanding payment to stop an ongoing attack
- Competitive interference: disabling services during critical business windows
- Political or ideological campaigns: targeting public-facing platforms for visibility
- Diversion tactics: overwhelming systems to distract from other simultaneous exploits
Regardless of the motivation, the goal remains the same: making a service slow, unstable, or completely unavailable to legitimate users. Understanding this objective makes it easier to see how attackers design and execute DDoS campaigns.
How Does a DDoS Attack Work?
A DDoS attack disrupts a service by coordinating traffic from many compromised devices to overwhelm a target server or network. Attackers typically build and control a botnet, directing thousands or even millions of infected systems to send requests to the same destination at the same time.
Most DDoS attacks follow a similar process that unfolds in four stages:
1. Botnet Creation
Attackers first compromise vulnerable internet-connected devices using malware. The compromised devices, which may include routers, IoT systems, or cloud servers, become part of a remotely controlled botnet.
2. Centralized Coordination
A command-and-control (C&C) system sends instructions to the botnet, specifying the attack target and method. The attacker may choose to strike the network layer or generate application-level requests.
3. Traffic Generation
After activation, the compromised devices simultaneously send large volumes of malicious traffic, ranging from connection floods to requests that resemble legitimate user activity. Techniques such as DNS amplification attack exploits that increase traffic impact by triggering large responses from third-party servers.
4. Resource Exhaustion
As traffic accumulates, bandwidth, CPU, memory, and connection limits are consumed. When these resources are saturated, legitimate users can no longer access the service.
How to Identify a DDoS Attack?
A DDoS attack is usually identified through abnormal traffic patterns and sudden pressure on infrastructure rather than a single clear error. When large volumes of coordinated requests begin to overwhelm network capacity or server resources, service performance quickly degrades.
Common signs of a DDoS attack include:
-
Unexpected traffic spikes
A rapid surge in requests or bandwidth usage without a clear business reason, such as a campaign or product launch. -
Slow performance or service interruptions
Web pages load unusually slowly, connections time out, or users cannot access certain features or the entire website. -
Resource exhaustion
CPU, memory, or network capacity suddenly reaches critical levels and remains high. -
Unusual request behavior
Large volumes of repeated requests to specific endpoints, such as login pages or APIs, especially from widely distributed IP addresses.
Taken together, these signals typically indicate that incoming traffic is exceeding normal operational patterns, which is a common sign that a coordinated DDoS campaign may be underway.
How to Stop a DDoS Attack?
Stopping a DDoS attack begins with keeping services available while distinguishing malicious traffic from legitimate users. Because modern attacks often target multiple layers simultaneously and adapt in real time, mitigation must combine traffic analysis, filtering, and adaptive response to maintain uninterrupted service.
Detection and Traffic Assessment
Abnormal bandwidth spikes, sustained resource exhaustion, or concentrated requests to specific endpoints often indicate an active attack. Continuous traffic monitoring and log analysis provide the visibility needed to confirm malicious patterns.
Traffic Filtering and Application Protection
Mitigation focuses on separating malicious traffic without disrupting normal users. Common controls include:
- Rate limiting excessive requests
- Blocking IP sources associated with known threats
- Dropping malformed or spoofed packets
- Deploying WAFs to inspect and filter suspicious HTTP and HTTPS traffic
These mechanisms reduce pressure on infrastructure while preserving legitimate access.
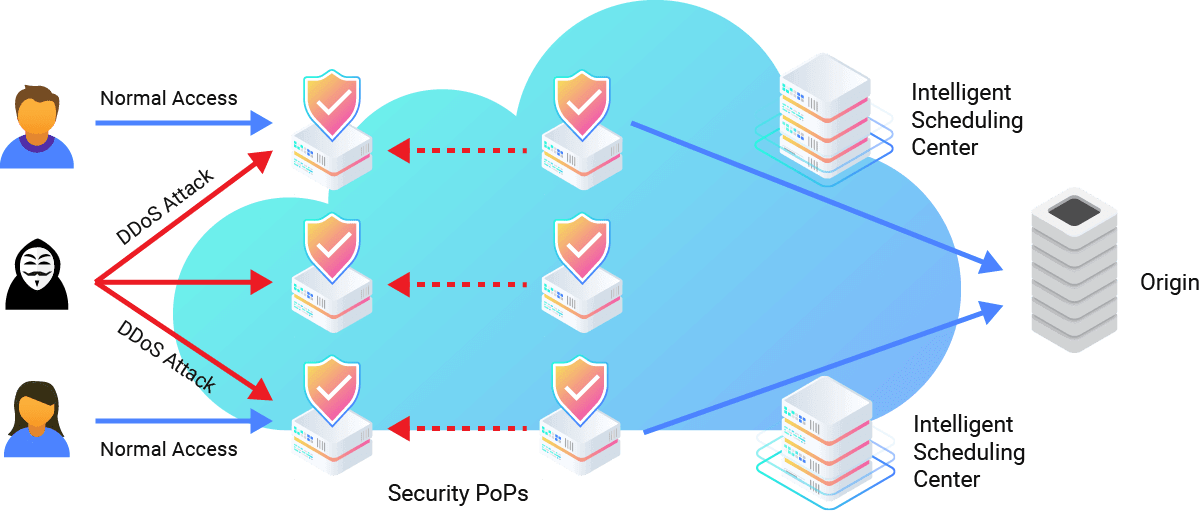
Upstream Scrubbing and Traffic Distribution
High-volume volumetric attacks must be handled before they reach the origin server. Scrubbing centers analyze and cleanse incoming data streams, forwarding only validated traffic downstream. Distributed edge infrastructure further disperses traffic loads to prevent localized saturation.
CDNetworks’ Flood Shield 2.0 integrates network-layer filtering, distributed scrubbing capabilities, and application-layer defense to mitigate attacks such as SYN floods, UDP floods, and HTTP floods while maintaining service continuity.
Adaptive Mitigation
As DDoS patterns can shift during an incident, effective protection relies on real-time traffic analysis and dynamic rule adjustments. Adaptive mitigation ensures that filtering strategies evolve alongside attack behavior.
DDoS Attacks FAQs
What Is a DDoS Attack and How Does It Work?
A Distributed Denial of Service (DDoS) attack is a cyberattack that overwhelms a target system with traffic from multiple sources. It works by exhausting bandwidth, server resources, or application processes, so legitimate users cannot access the service.
Which Industries Are Most Targeted by DDoS Attacks?
Industries that rely heavily on online availability are most frequently targeted, including e-commerce, financial services, gaming, SaaS platforms, telecommunications, and public sector organizations.
What Are the Latest Trends in DDoS Attacks?
DDoS attacks are becoming more sophisticated and harder to block. Attackers often use multi-vector campaigns combining large network floods with Layer 7 traffic. IoT-based botnets generate massive volumes, helping attackers bypass simple defenses and prolong disruption.
What Is Layer 7 DDoS Protection?
Layer 7 DDoS protection defends web apps and APIs from attacks that mimic legitimate users. Since these attacks use valid HTTP/HTTPS requests, simple filtering fails. Effective defense combines rate limiting, traffic profiling, and WAFs to detect abnormal patterns while allowing legitimate access.
Can DDoS Attacks Be Stopped?
Yes. While no system can eliminate risk entirely, layered mitigation strategies that combine traffic filtering, scrubbing centers, application-layer protection, and continuous monitoring can effectively stop or significantly reduce the impact of DDoS attacks. Solutions like CDNetworks Flood Shield 2.0 implement these strategies, providing automated protection and real-time threat mitigation for web applications and networks.
