Table of Contents
What Is a DDoS Attack?
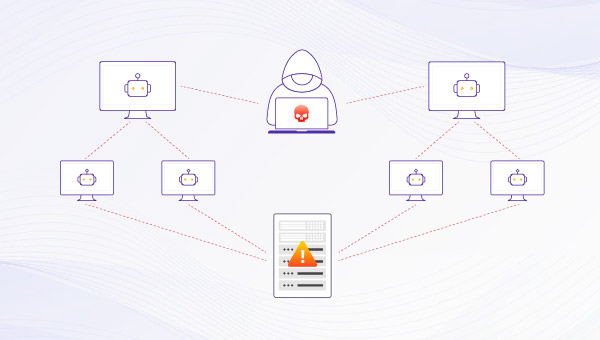
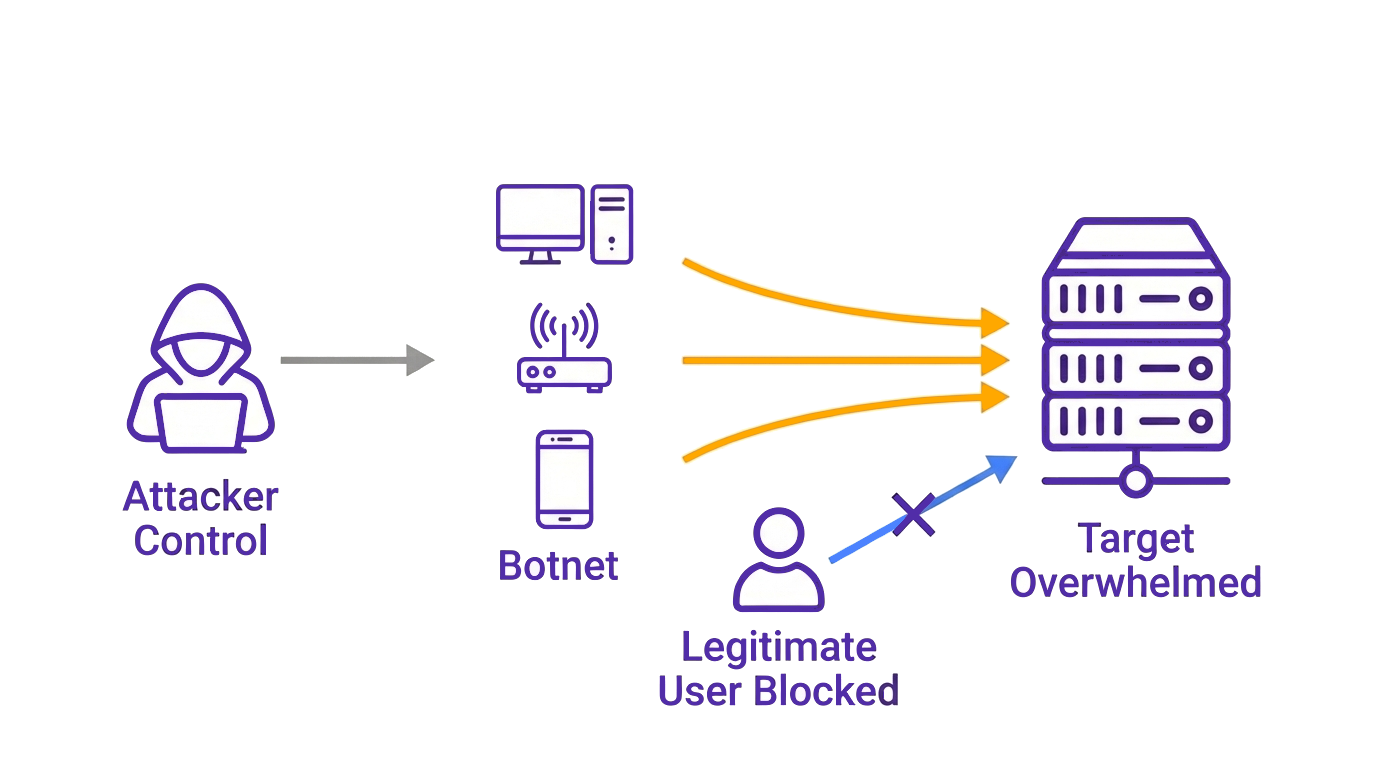
A DDoS attack, also known as a distributed denial of service, is a type of cyber threat designed to disrupt online services by overwhelming systems until normal access becomes impossible. Instead of relying on a single source, attackers coordinate traffic from a large number of compromised devices (botnets), sending simultaneous requests to the same destination. The resulting surge consumes bandwidth and server resources, eventually preventing services from responding to legitimate users.
Types of DDoS Attacks
DDoS attacks are commonly grouped by which layer of a network they aim to overwhelm. The most widely recognized types of DDoS attacks fall into three categories:
-
Volumetric DDoS attacks overwhelm network capacity by flooding bandwidth at scale, preventing traffic from reaching backend systems in the first place.
-
Protocol DDoS attacks exhaust server resources by abusing how connections are established and maintained, rather than relying on sheer traffic volume.
-
Application-layer DDoS attacks, often referred to as a layer 7 DDoS attack, target applications directly, overwhelming services with large numbers of HTTP requests that closely resemble normal user behavior.
Each type of DDoS attack disrupts availability in a different way, which directly affects how a DDoS attack unfolds.
DDoS vs. DoS Attacks: Key Differences
While a Denial of Service (DoS) attack overwhelms a service using traffic from one source, a DDoS attack applies the same pressure from many compromised devices at once.
The difference lies in scale, traffic origin, and how difficult the attack is to detect and contain:
| Dimensions | DDoS | DoS |
|---|---|---|
| Traffic source | Many compromised devices | One device |
| Attack scale | Large and distributed | Limited |
| Detection difficulty level | Much higher | Relatively low |
| Impact on availability | Widespread and sustained | Short and localized |
How Does a DDoS Attack Work?
A DDoS attack works by coordinating traffic from many sources to overwhelm a single target. Attackers typically begin by assembling a network of compromised devices and directing them to send requests to the same service at the same time. Each device may generate only a small amount of traffic, but together they create a volume that targeted servers cannot process efficiently, leaving legitimate users unable to connect.
Once traffic reaches the target, different layers of the network stack are affected in different ways, from bandwidth saturation at the network layer to connection exhaustion at the transport layer and request handling strain at the application layer.
Some DDoS attacks rely on sheer traffic volume, such as volumetric attacks that flood bandwidth with amplified packets, often involving abuse of open DNS server responses to magnify traffic. Others focus on exhausting protocol resources through techniques like SYN floods and other protocol attacks. More advanced attacks operate at the application layer by repeatedly triggering actions such as page loads or API calls.
Attackers rarely rely on a single technique. Modern DDoS campaigns often shift methods during an active attack, as the attack includes multiple vectors that change based on defensive responses, adjusting traffic patterns, packet structures, or request rates to bypass static defenses.
Volume may spike suddenly, then drop into lower-rate flows designed to blend in with normal usage, making detection more difficult and prolonging disruption. Without visibility across layers and traffic sources, distinguishing malicious traffic from real users becomes increasingly challenging as the attack evolves.
How Long Does a DDoS Attack Last?
The length of a DDoS attack varies widely because it reflects an ongoing contest between attackers and defenders rather than a fixed timeline. Once an attack begins, its duration depends on how quickly defensive controls can respond to shifting traffic patterns and attack techniques.
Some attacks last only a few minutes and are designed to test response thresholds or trigger a brief service of disruption. Others continue for hours or even days when attackers adapt their methods after initial defenses take effect, rotating sources or switching attack vectors to maintain pressure on the target.
Attack objectives also influence how long an attack persists. Short campaigns may aim to probe weaknesses or create temporary outages, while prolonged attacks often target sustained downtime, revenue loss, or reputational damage, especially customer-facing services.
Defensive readiness plays a decisive role. When mitigation systems identify malicious traffic early and respond effectively, attacks lose impact quickly. In less prepared environments, attackers gain time to blend malicious traffic with legitimate users and extend disruption.
Over time, the cost of maintaining an attack rises, and once defenses force diminishing returns, many campaigns slow down or stop altogether. In practice, the duration of a DDoS attack often reveals more about a target’s resilience than the attacker’s initial scale.
How to Prevent a DDoS Attack
Preventing a DDoS attack focuses on reducing exposure before traffic becomes disruptive. Since attacks evolve across layers and shift tactics in real time, effective prevention relies on preparation, visibility, and scalable defenses rather than a single control.
Key prevention measures typically include:
-
Continuous traffic monitoring to establish normal behavior and quickly spot anomalies before services degrade.
-
Basic security hygiene, such as hardened credentials and patched systems, to reduce exploitable weaknesses attackers often target.
-
Traffic controls and thresholds, including rate limiting and filtering, to slow early attack waves and protect critical resources.
-
Up-to-date security infrastructure, ensuring network security tools and Web Application Firewall (WAF) policies remain effective as attack methods evolve.
-
Adequate capacity and redundancy, which helps absorb sudden spikes caused by volumetric attack traffic.
-
Distributed protection through CDN and cloud-based defenses, allowing traffic to be dispersed and filtered closer to its source.
-
A defined response plan, so teams can act immediately once malicious traffic appears instead of reacting under pressure.
No single measure can prevent every DDoS attack. In practice, prevention works best as a layered strategy that limits attack impact early and preserves availability for legitimate users.
How Can CDNetworks Help Stop DDoS Attacks?
Once a DDoS attack is underway, the priority shifts from simply blocking traffic to keeping services accessible. Traffic surges may arrive from multiple vectors at the same time, while request patterns change rapidly as attackers probe for weaknesses. In these conditions, static defenses and on-promises capacity are often unable to respond quickly enough, especially when attacks target multiple layers of the network simultaneously.
For businesses under active attack, CDNetworks provides cloud-based DDoS mitigation through Flood Shield 2.0. Incoming traffic is routed through globally distributed Points of Presence (PoPs), where traffic is analyzed and filtered before it reaches the origin server.
Flood Shield 2.0 addresses modern DDoS attack scenarios through the following capabilities:
-
Protection Across All DDoS Attack Vectors
Flood Shield 2.0 mitigates volumetric, protocol, and Layer 7 DDoS attacks using layered, behavior-based controls at the network edge. -
20+ Tbps Global Scrubbing Capacity
Distributed scrubbing centers absorb large-scale traffic floods early, preventing bandwidth saturation and infrastructure overload. -
Adaptive, AI-Driven Defense
Real-time traffic profiling and machine learning continuously adjust mitigation policies as attack patterns evolve. -
Integrated WAAP Protection
DDoS mitigation operates alongside Web Application Firewall, bot management, and API security to protect application logic and exposed interfaces. -
Globally Distributed Infrastructure
A wide PoP footprint disperses attack traffic close to its source, reducing latency and avoiding single points of congestion. -
Cloud-Based, Always-On Operation
Continuous monitoring and automated response eliminate delays associated with manual activation or hardware-based defenses. -
24/7/365 Security Support
Dedicated security teams monitor attacks around the clock and assist throughout the detection and mitigation phases.
As modern DDoS attacks shift tactics in real time, effective defense depends on adaptive mitigation rather than static blocking. Maintaining availability under sustained pressure requires visibility across layers, distributed capacity, and the ability to respond dynamically as attack behavior changes.
DDoS Attacks FAQs
What Is a DDoS Attack?
A Distributed Denial of Service (DDoS) attack disrupts online services by flooding targeted servers or networks with traffic from many compromised devices. The distributed structure increases attack volume and makes filtering more difficult than single-source attacks.
What Is the Difference Between DoS and DDoS Attacks?
A DoS attack comes from a single source, while a DDoS attack uses multiple devices operating simultaneously. The distributed approach allows DDoS attacks to scale faster and resist basic blocking methods.
How Do DDoS Attacks Work?
DDoS attacks work by coordinating large numbers of devices to send connection requests or HTTP requests toward targeted servers. Attack traffic may target bandwidth, network protocols, or application behavior to disrupt access for legitimate users.
What Happens During a Live DDoS Attack?
During a live DDoS attack, malicious traffic competes with legitimate traffic for network and server resources. As resources are exhausted, legitimate users experience slow responses or complete service disruption.
How Long Do DDoS Attacks Last?
DDoS attacks may last from a few minutes to several days. Duration depends on attacker objectives, attack complexity, and how quickly mitigation measures are activated.