AI Threat Detection
AI Threat Detection
What Is AI Threat Detection
AI threat detection refers to the use of artificial intelligence (AI) technologies to identify, analyze, and respond to cybersecurity threats in real time. These technologies include machine learning (ML), natural language processing (NLP), and behavioral analytics. AI systems constantly learn from data patterns, allowing them to identify both known and emerging threats with greater accuracy.
At its core, AI-driven threat detection systems process vast amounts of data. They use data to uncover anomalies, suspicious behaviors, and potential attack vectors. This makes them particularly effective in modern environments where threats evolve rapidly and attack surfaces are increasingly complex.
How AI Performs Threat Detection
AI threat detection tools rely on multiple interconnected processes that support full threat detection and response capabilities:
Data Collection and Aggregation
AI systems gather data from multiple sources, including networks, endpoints, cloud environments, and logs. This data forms the foundation for identifying threats across the entire attack surface.
Pattern Recognition with Machine Learning
Machine learning models analyze historical and real-time data to identify patterns associated with normal and malicious behavior. This is the foundation of modern machine learning threat detection systems.
Behavioral Analysis
AI establishes baselines for normal system and user behavior. Any deviation, such as unusual login times or abnormal data transfers, can trigger alerts for potential threats.
Continuous Monitoring of Environments
AI systems are constantly monitoring cloud workloads, endpoints, and network traffic to identify malicious activities in real time.
Natural Language Processing for Threat Intelligence
Natural Language Processing (NLP) helps AI analyze unstructured data such as reports, security feeds, and forums to detect emerging threats and vulnerabilities.
Automating Responses
AI systems can automatically respond to threats by taking actions such as isolating compromised devices or blocking suspicious traffic.
In modern environments, agentic AI is also emerging as a new layer of autonomy, where AI systems can independently investigate threats and take adaptive actions with minimal human input.
AI-powered Threat Detection vs. Traditional Threat Detection
| Aspect | AI Threat Detection | Traditional Threat Detection |
|---|---|---|
| Detection Method | AI models, anomaly detection, ML-based analysis | Rule-based and signature-based |
| Adaptability | Continuously learns from new data | Requires manual updates |
| Threat Coverage | Detects unknown and advanced threats | Limited to known threats |
| Responses | Automated or semi-automated | Mostly manual |
| Scalability | Handles cloud-scale environment | Limited scalability |
| Data Processing | Use vast amounts of data from multiple sources | Relies on narrower data inputs |
As shown above, AI-driven systems significantly improve security operations by enabling faster, smarter, and more adaptive defense mechanisms.
Benefits of AI-driven Threat Detection
Faster Detection Across Complex Environments
AI-powered tools analyzes data in real time, enabling organizations to quickly detect threats across distributed systems and cloud environments.
Proactive Defense Against Advanced Threats
By identifying anomalies early, AI helps prevent advanced threat actors from exploiting vulnerabilities.
Reduced False Positives
One of the key advantages of AI is its ability to reduce false positives, allowing security teams to focus on genuine threats rather than noise.
Improved Use of Human Expertise
AI enhances rather than replaces human expertise, allowing security professionals to focus on investigation and strategy instead of repetitive monitoring.
Stronger Protection of Sensitive Data
AI systems help safeguard sensitive data by detecting unauthorized access, leaks, and abnormal data movement patterns.
Improved Security Operations Efficiency
By automating detection, classification, and response workflows, AI significantly improves overall security operations efficiency.
Challenges and Limitations
Despite its advantages, AI-driven threat detection also comes with certain challenges and limitations:
False Positives and Model Limitations
AI systems can still generate false positives. This often happens in early deployment stages when models are not fully trained on environment-specific data.
Security Risks in AI Systems
AI systems are also potential targets for attackers. Attackers may try to change models or exploit flaws in AI security tools.
Data Bias
Biased or incomplete training data can lead to inaccurate predictions. As a result, the system may miss some threats and incorrectly flag normal activity as malicious.
Technical and Operational Complexity
AI implementation requires significant computational resources, skilled personnel, and continuous tuning to maintain effectiveness in dynamic environments.
Applying AI Threat Detection in Real-World Security
Understanding how AI-powered threat detection works is only part of the equation. In practice, organizations need solutions that can apply these capabilities effectively at scale.
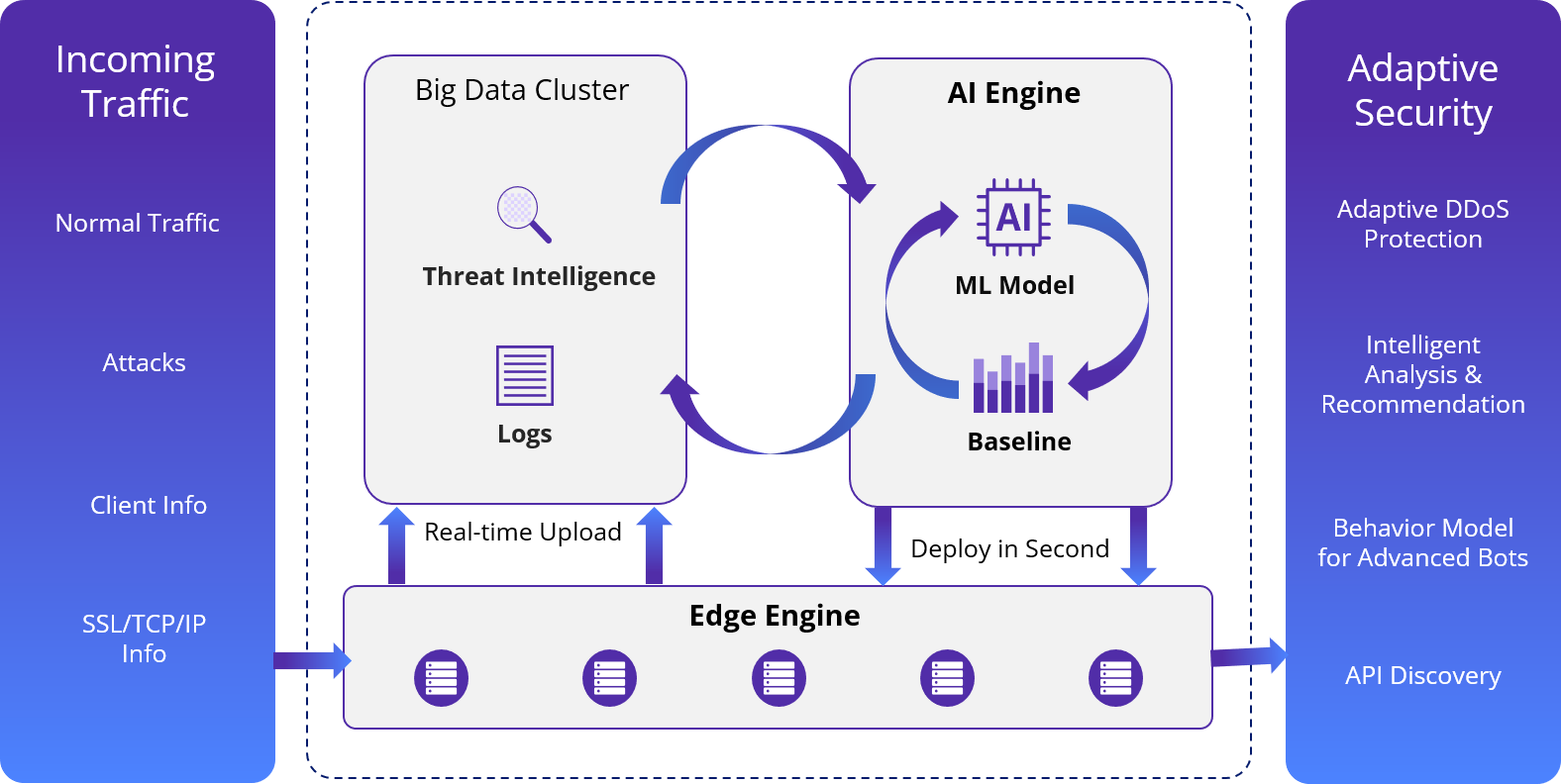
CDNetworks integrates AI deeply into its security solutions, leveraging advanced machine learning and behavioral analytics to deliver robust, real-time protection. By embedding AI into its architecture, CDNetworks enables organizations to detect and mitigate sophisticated threats more efficiently.
Its AI-powered capabilities help defend against a wide range of cyber threats like zero-day attacks, automated bot attacks, and advanced persistent threats. Continuous learning and global threat intelligence further improve detection accuracy and response speed.
As a result, organizations can maintain a more adaptive security posture that evolves alongside emerging threats, helping to protect web applications, APIs, and broader digital infrastructure.
To explore how AI-driven threat detection can strengthen your security posture, contact CDNetworks for tailored solutions.
FAQ
How does AI improve threat detection?
AI improves threat detection by learning normal behavior patterns from data, then detecting deviations in real time using machine learning and behavioral analytics, and automatically correlating signals to identify potential threats.
What types of threats can AI detect?
AI can detect many types of threats, including malware, phishing, insider threats, zero-day exploits, and bot attacks. It can also identify abnormal user behavior across networks, endpoints, and cloud environments.
What role can large language models (LLMs) play in threat detection?
Large language models process unstructured threat intelligence, analyze security reports, and assist in identifying emerging attack patterns and vulnerabilities.
Is AI threat detection accurate?
Accuracy depends on data quality and model training, with well-optimized systems significantly reducing false positives while improving detection of complex threats.
